BloodHound ⚙️
Theory
BloodHound (Javascript webapp, compiled with Electron, uses Neo4j as graph DBMS) is an awesome tool that allows mapping of relationships within Active Directory environments. It mostly uses Windows API functions and LDAP namespace functions to collect data from domain controllers and domain-joined Windows systems.
Practice
Collection
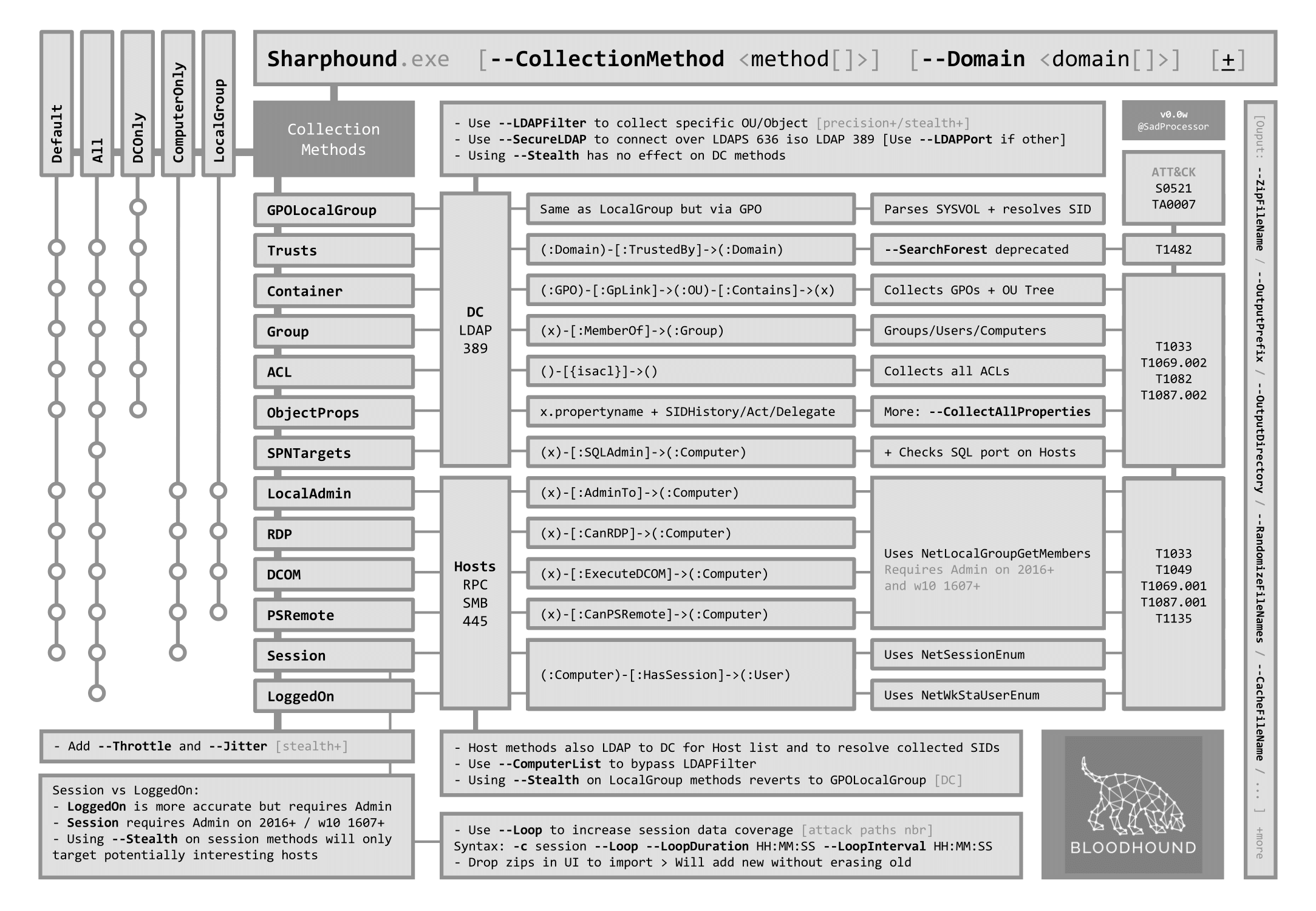
BloodHound needs to be fed JSON files containing info on the objects and relationships within the AD domain. This information are obtained with collectors (also called ingestors). The best way of doing this is using the official SharpHound (C#) collector.
SharpHound (sources, builds) is designed targeting .Net 4.5. It can be used as a compiled executable.
It must be run from the context of a domain user, either directly through a logon or through another method such as runas (runas /netonly /user:$DOMAIN\$USER) (see Impersonation). Alternatively, SharpHound can be used with the LdapUsername and LdapPassword flags for that matter.
SharpHound.exe --collectionmethods AllWhen running SharpHound from a runas /netonly-spawned command shell, you may need to let SharpHound know what username you are authenticating to other systems as with the OverrideUserName flag
The previous commands are basic but some options (i.e. Stealth and Loop) can be very useful depending on the context
# Perform stealth collection methods
SharpHound.exe --collectionmethods All --Stealth
# Loop collections (especially useful for session collection)
# e.g. collect sessions every 10 minutes for 3 hours
SharpHound.exe --collectionmethods Session --Loop --loopduration 03:00:00 --loopinterval 00:10:00
# Use LDAPS instead of plaintext LDAP
SharpHound.exe --secureldapMore help on the CLI commands here.
Here are a few tips and tricks on the collection process
- Testers can absolutely run SharpHound from a computer that is not enrolled in the AD domain, by running it in a domain user context (e.g. with runas, pass-the-hash or overpass-the-hash). This is useful when domain computers have antivirus or other protections preventing (or slowing) testers from using enumerate or exploitation tools.
- When obtaining a foothold on an AD domain, testers should first run SharpHound with all collection methods, and then start a loop collection to enumerate more sessions.
Analysis
Once the collection is over, the data can be uploaded and analyzed in BloodHound by doing the following.
- Find paths between specified nodes
- Run pre-built analytics queries to find common attack paths
- Run custom queries to help in finding more complex attack paths or interesting objects
- Run manual neo4j queries
- Mark nodes as high value targets for easier path finding
- Mark nodes as owned for easier path finding
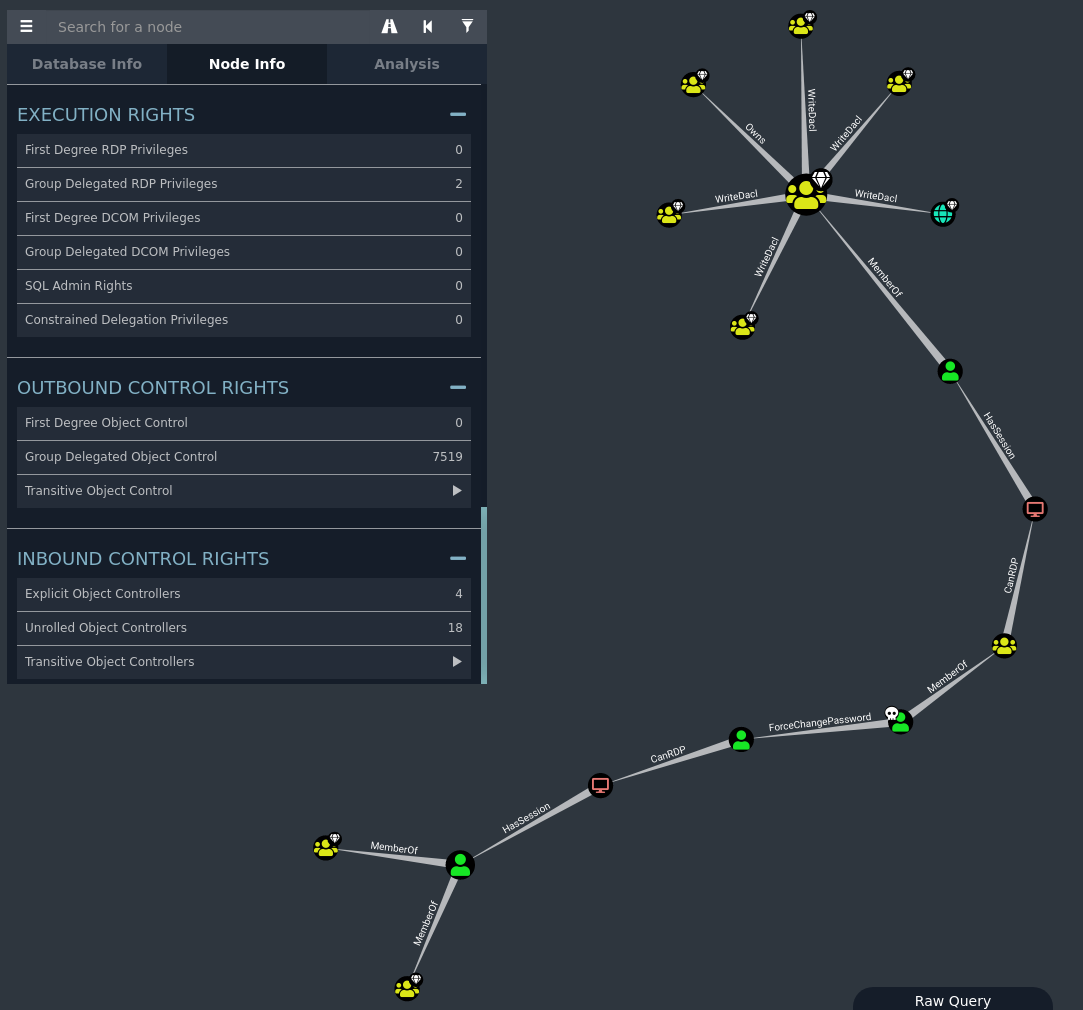
- Find information about selected nodes: sessions, properties, group membership/members, local admin rights, Kerberos delegations, RDP rights, outbound/inbound control rights (ACEs), and so on
- Find help about edges/attacks (abuse, OPSEC considerations, references)
Using BloodHound can help find attack paths and abuses like ACEs abuse, Kerberos delegations abuse, credential dumping and credential shuffling, GPOs abuse, Kerberoast, ASREProast, domain trusts attacks, etc.
For detailed and official documentation on the analysis process, testers can check the following resources: the BloodHound GUI, nodes and edges.
Some custom queries can be used to go even further with the analysis of attack paths, such as Exegol's custom queries.
Here are some examples of quick wins to spot with BloodHound
- shadow admins: users that are not members of privileged Active Directory groups but have sensitive privileges over the domain (run graph queries like "find principals with DCSync rights", "users with most local admin rights", or check "inbound control rights" in the domain and privileged groups node info panel)
- other over-privileged users: user that can control many objects (ACEs) and that often leads to admins, shadow admins or sensitive servers (check for "outbound control rights" in the node info panel)
- over-privileged computers: find computers that can do (un)constrained Kerberos delegation (run graph queries like "find computer with unconstrained delegations")
- admin computers: find computers (A) that have admin rights against other computers (B). This can be exploited as follows: computer A triggered with an MS-RPRN abuse (printerbug), authentication is then relayed, and credentials are dumped on the computer B.
Other quick wins can be easily found with the bloodhound-quickwin Python script
bhqc.py -u $neo4juser -p $neo4jpasswordCrackHound (Python) can be used to populate BloodHound's database with password obtained during a pentest. This can help sort and report attack paths.
Resources
https://github.com/SadProcessor/HandsOnBloodHound/blob/master/BH21/BH4_SharpHound_Cheat.pdf
https://blog.riccardoancarani.it/bloodhound-tips-and-tricks/
https://bloodhound.readthedocs.io/en/latest/
https://porterhau5.com/blog/extending-bloodhound-track-and-visualize-your-compromise/
